
When everything is transforming digitally – from your industry to the threats you face – you need access management solutions designed to outpace any security risks that challenge your ability to compete.
Learn MoreIncreased investment in traditional endpoint security has failed to reduce the number of successful attacks. Foundational endpoint privilege controls are needed to remove local admin rights, enforce least privilege, protect credentials and defend against ransomware.
Learn More

Protect privileged access across all identities, infrastructures and apps, from the endpoint to the cloud.
Learn MoreSecrets and other non-human credentials, which are used by all types of applications to access IT resources and digital supply chains, are increasingly targeted by cyberattackers and are at risk of being inadvertently exposed. With CyberArk, security teams can centrally secure credentials across application portfolios and DevOps pipelines while giving developers a frictionless experience.
Learn More

Poor visibility, inconsistent tooling and a proliferation of human and machine identities create significant identity security challenges in the public cloud. CyberArk helps cloud security teams consistently analyze, secure and monitor both standing and just-in-time privileged access in hybrid and multi-cloud environments.
Learn MoreBusinesses leaders and IT teams are under increased pressure to ensure that only the right people have the right access to corporate resources. As a result, they can no longer rely on manual and error-prone processes to assign, manage and audit user privileges. With CyberArk, organizations can orchestrate and automate all aspects and processes related to the administration and governance of the digital identity lifecycle.
Learn More

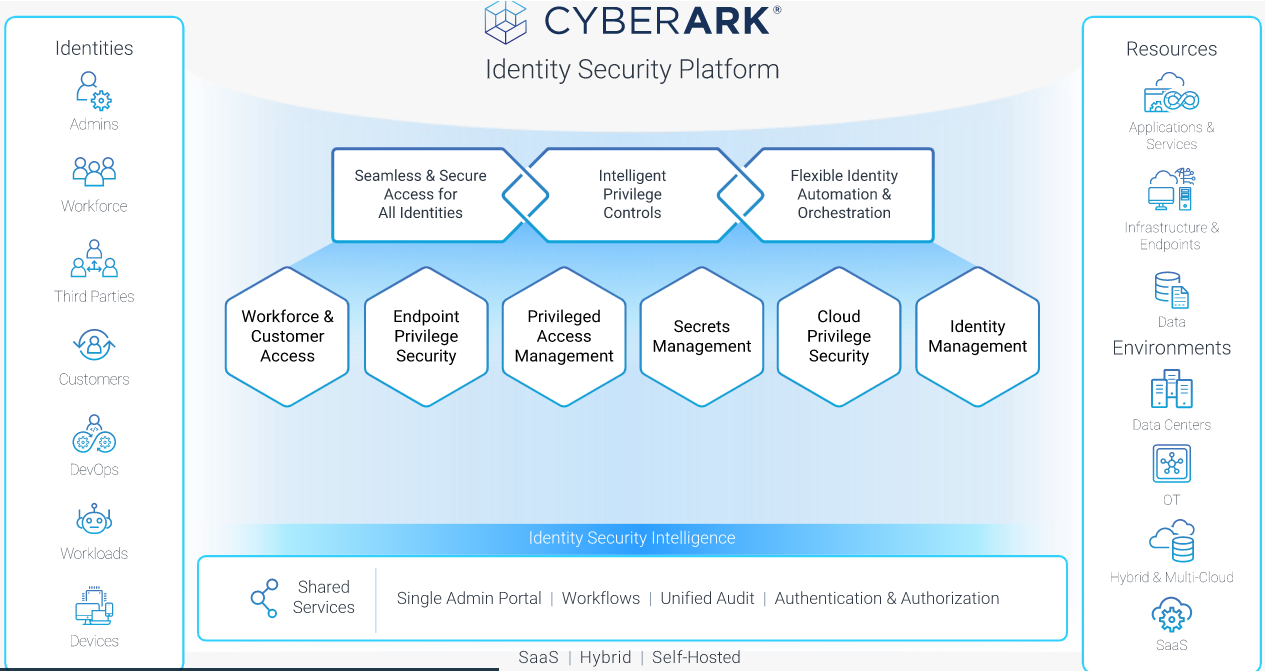
The Identity Security Platform Shared Services enable operational efficiencies, leveraging a single admin portal with unified audit and Identity Security Intelligence. With Identity Security Intelligence, customers can leverage continuous identity threat detection and response to deliver measurable cyber risk reduction and enable zero trust.
Learn MoreCentered on intelligent privilege controls, Identity Security seamlessly secures access for all identities and flexibly automates the identity lifecycle with continuous threat detection and prevention — all with a unified approach.